Documentation Index
Fetch the complete documentation index at: https://docs.cloudcapital.co/llms.txt
Use this file to discover all available pages before exploring further.
Time to complete: ~30 minutes
- Forecasting role — required by all customers. Read-only access to your CUR data and AWS pricing APIs.
- Optimization role — required only if you are using Cloud Capital to manage commitments and Savings Plans on your behalf. Applied exclusively to a dedicated, empty AWS account created in your AWS Organization used for purchasing on your behalf — never to your management or workload accounts.
Part 1: Connect your AWS cost data (all customers)
What Cloud Capital accesses
The Forecasting CloudFormation template creates a read-only IAM role. Cloud Capital uses this role to:| Purpose | AWS Services Used |
|---|---|
| Read your Cost and Usage Report from S3 | s3:GetObject, s3:ListBucket — scoped to your specific CUR bucket only |
| Look up current AWS pricing for Savings Plans and Reserved Instances | pricing:GetProducts, savingsplans:Describe* |
| Discover commitment offerings available in your account | rds:Describe*, elasticache:Describe*, redshift:Describe*, es:Describe*, ec2:Describe* |
| Enumerate accounts in your AWS Organization | organizations:List*, organizations:Describe* |
| Read cost, billing, and utilization data | ce:Get*, billing:Get*, and related read-only billing APIs |
The Forecasting role is strictly read-only. No actions that create, modify, or delete any AWS resources are included. Cloud Capital cannot make any changes to your AWS environment through this role.
Setup
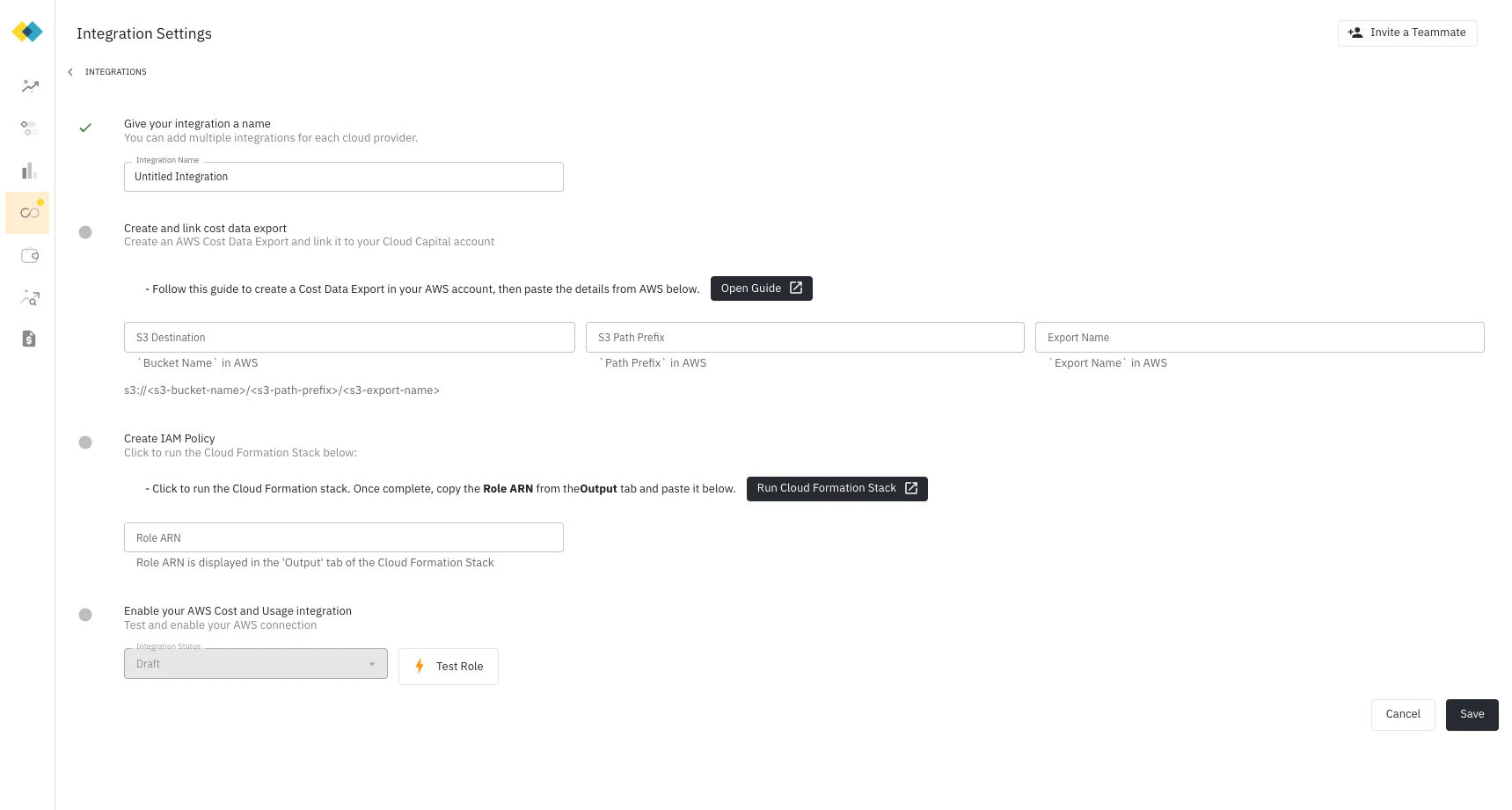
Create a new Integration in Cloud Capital
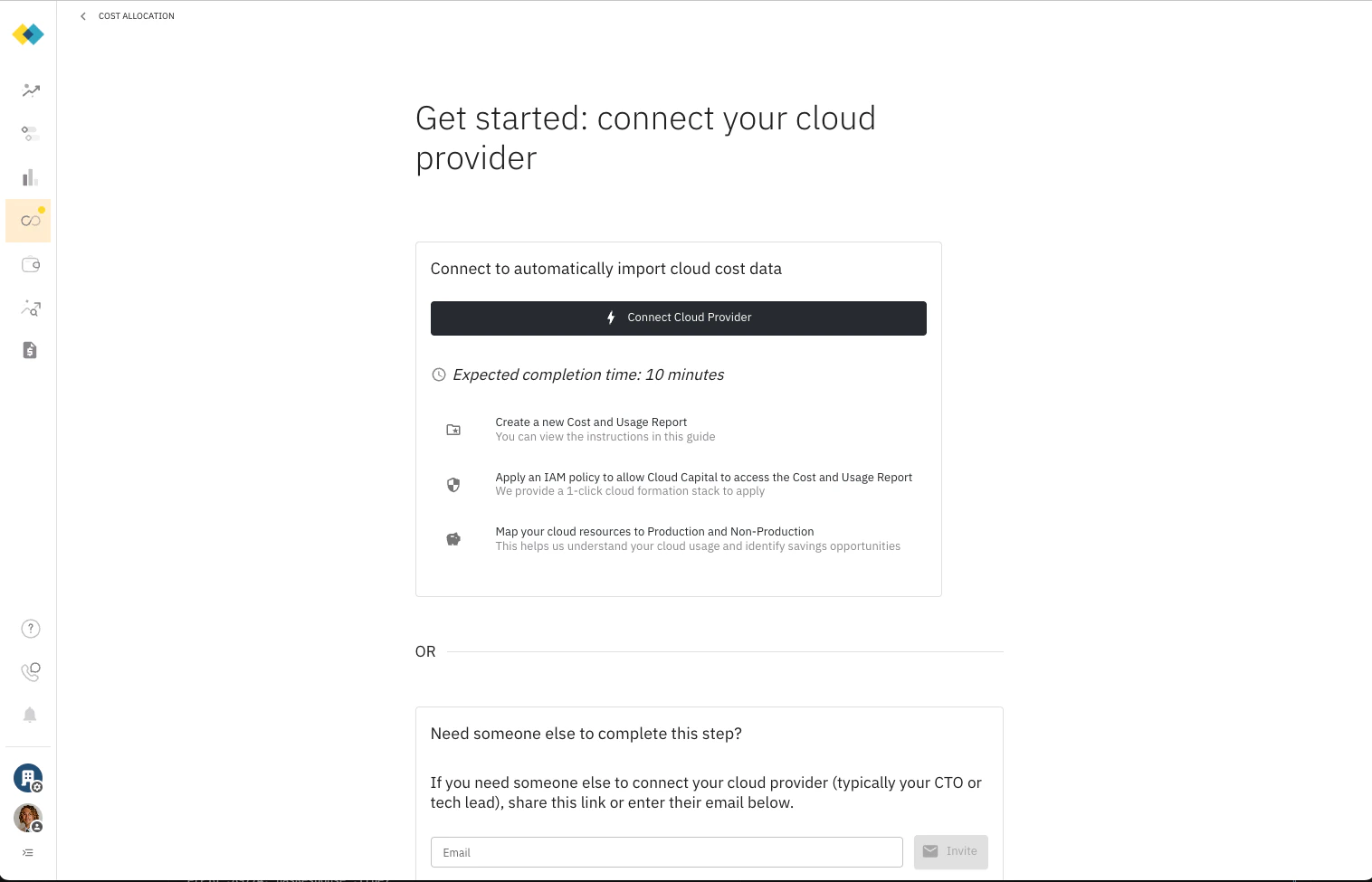
From the main dashboard, navigate to Cost Allocation and click Connect Cloud Provider.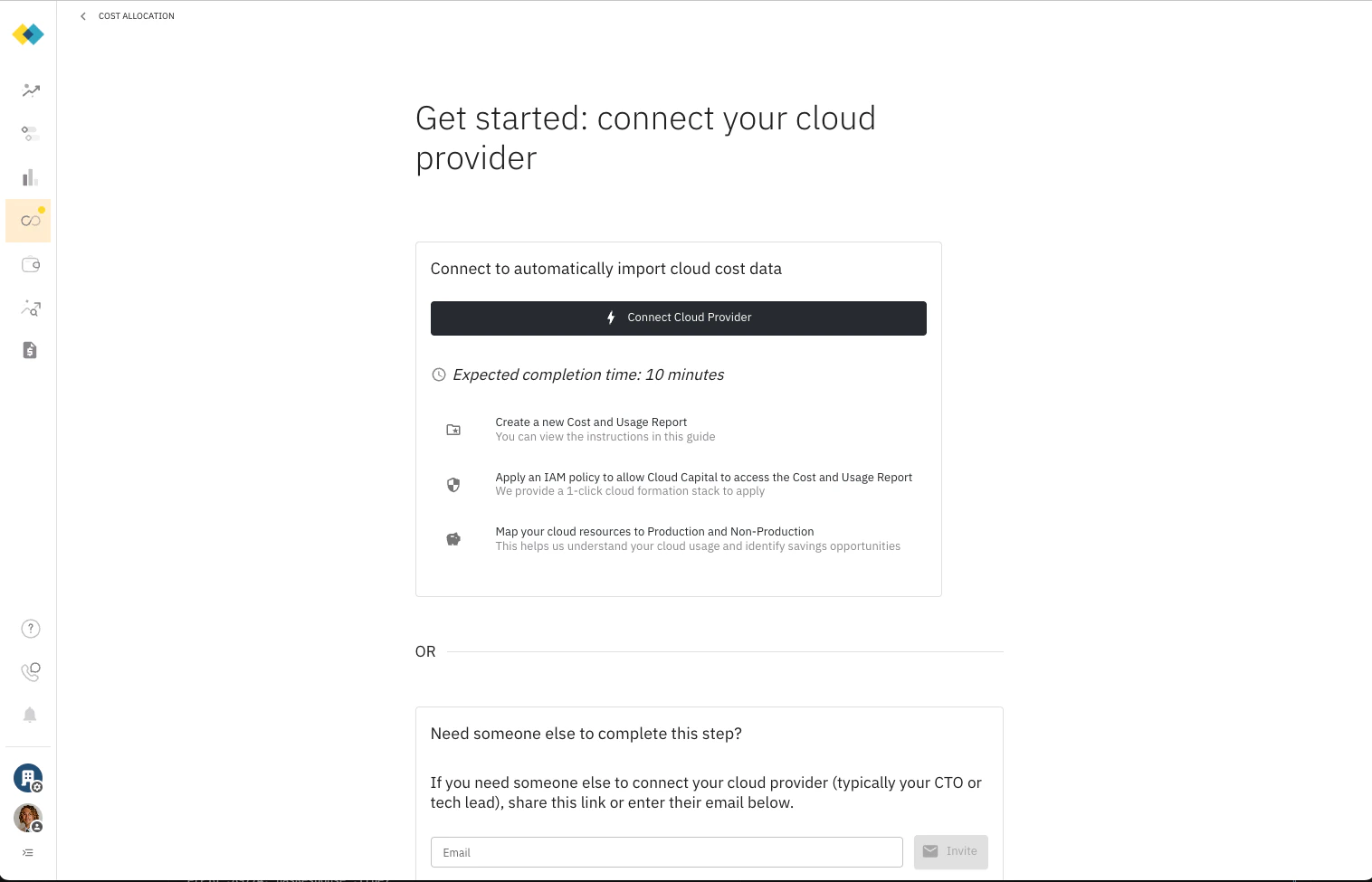
AWS).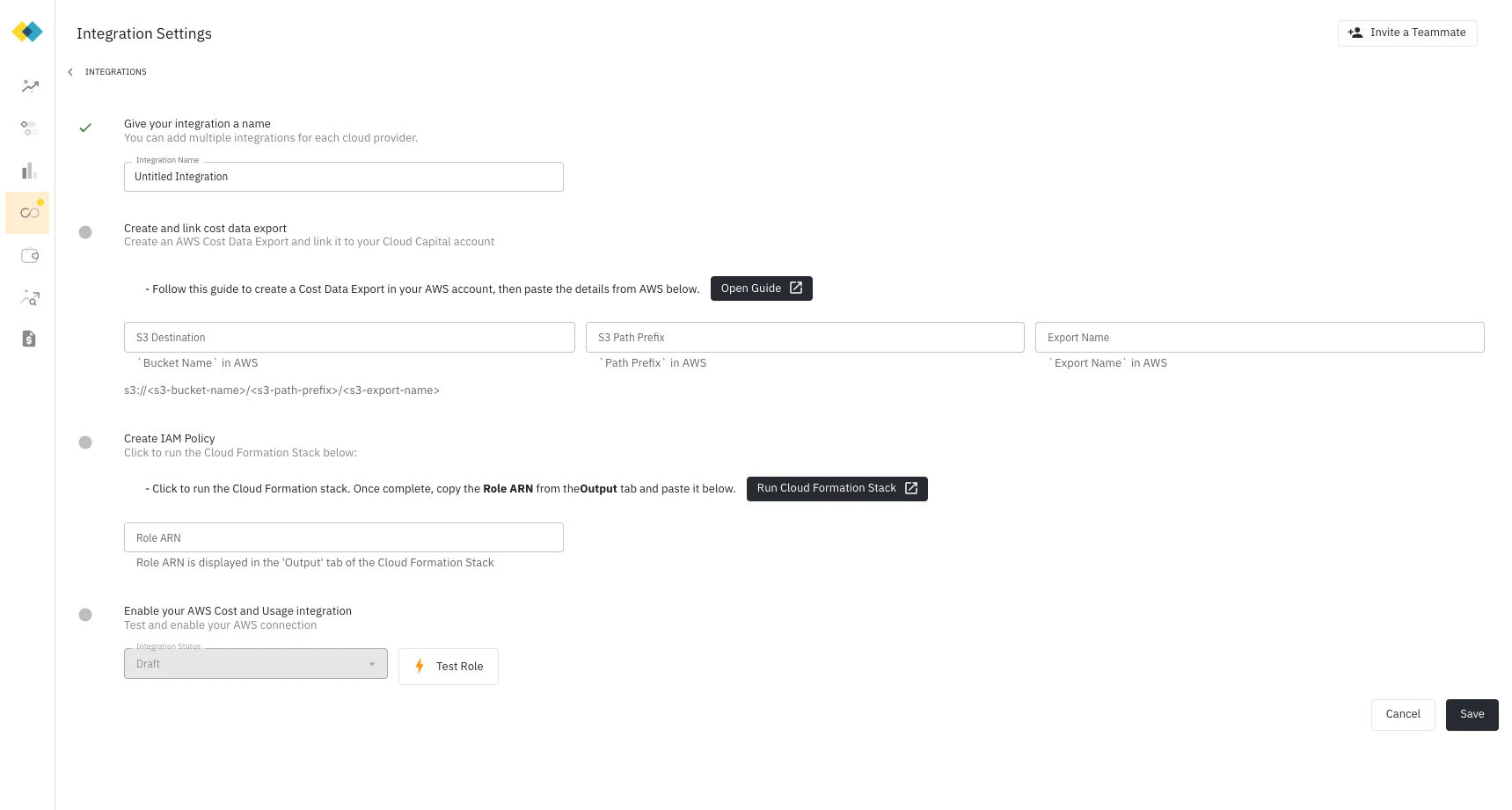
Create a cost data export in AWS
This step walks you through creating a cost data export in the AWS Billing and Cost Management portal.
If you already have a daily CUR 2.0 export running with the settings below, you can use the existing bucket and skip ahead to the next step.
- In the AWS console, navigate to Billing and Cost Management
- Click Data Exports on the left, then click Create
- Select Standard data export
- Give the report a name (e.g.,
cloud-capital-cost-export) — you will enter this name in Cloud Capital
- Format: CUR 2.0 (default)
- Include resource IDs: No (leave unchecked)
- Split cost allocation data: No (leave unchecked)
- Time granularity: Hourly
- Column selection: keep the default
- Compression type and file format: Parquet - Parquet
- File versioning: Overwrite existing data export file
- Choose Configure → Create a bucket (recommended), or select an existing bucket
-
Add an S3 path prefix of
hourly-export
You will need the S3 destination (bucket name + path prefix + export name) in the next step. It is shown directly after creating the report — copy and paste it.
Add cost data export settings to Cloud Capital
Copy and paste the Bucket Name, Path Prefix, and Export Name from the previous step into the Integration settings in Cloud Capital.
Create the Forecasting IAM role
Under Create IAM Policy, click Run Cloud Formation Stack. Cloud Capital pre-populates the required parameters in the stack — you do not need to enter them manually. This creates a read-only IAM role in your AWS Payer or Management account, scoped to your specific CUR bucket.Once the stack completes, AWS provides a Role ARN. Enter this Role ARN in Cloud Capital.You can review the full policy: aws-cloudformation-forecasting.json
Test and enable your integration
Click Test Role to verify that Cloud Capital can access the bucket. If the connection is successful, your Integration status changes to Enabled. Save your integration to activate it.
AWS typically takes 24–48 hours to populate the Cost and Usage Report for the first time. After 24 hours, return to the Integration settings to verify that data is being imported before proceeding.
Part 2: Enable Commitment Optimization (commitment customers only)
This section applies only if Cloud Capital will be purchasing and managing AWS Savings Plans and Reserved Instances on your behalf. Forecasting-only customers do not need to complete this part.What Cloud Capital accesses
The Optimization CloudFormation template creates a second IAM role that allows Cloud Capital to purchase and manage AWS commitments on your behalf.AWS Savings Plans and Reserved Instances purchased in a payer or management account automatically distribute their discount benefit across all linked accounts in the Organization. Using a dedicated empty account for purchasing is the recommended AWS pattern — it keeps commitment purchasing isolated from your workload accounts while still allowing the discounts to flow through to your entire Organization.
| Purpose | AWS Services Used |
|---|---|
| Purchase and manage Savings Plans | savingsplans:* |
| Purchase EC2 Reserved Instances | ec2:PurchaseReservedInstancesOffering and related EC2 RI actions |
| Purchase RDS, Redshift, ElastiCache, and OpenSearch Reserved Instances | rds:PurchaseReservedDbInstancesOffering, redshift:PurchaseReservedNodeOffering, elasticache:PurchaseReservedCacheNodesOffering, es:PurchaseReservedInstanceOffering |
| Create service-linked roles required by AWS during first purchase | iam:CreateServiceLinkedRole |
| Manage service quota increases when required | servicequotas:*, support:* |
Setup
Prepare a dedicated commitment account
Cloud Capital requires a dedicated, empty AWS account for commitment purchasing. This account should contain no workloads and exist solely for this purpose. If you do not already have one, create a new account in your AWS Organization before proceeding.
Deploy the Optimization CloudFormation stack
In the dedicated commitment account, deploy the Optimization CloudFormation template. As with the Forecasting stack, Cloud Capital pre-populates the required parameters when you click Run Cloud Formation Stack — you do not need to enter them manually.Once the stack completes, AWS provides a Role ARN. Share this with your Cloud Capital contact to complete the setup.
How the cross-account role works
Both roles use AWS’s standard cross-account access pattern with an ExternalId condition. Cloud Capital’s AWS account ID and your unique ExternalId are embedded in each role’s trust policy at setup time — meaning only Cloud Capital’s specific AWS account can assume the role, and only when presenting the correct ExternalId. This prevents confused deputy attacks. You can revoke either role at any time by deleting the corresponding CloudFormation stack in your AWS console, which immediately removes Cloud Capital’s access. This is a well-established AWS pattern for granting third-party access. For more detail on how cross-account roles and ExternalId conditions work, see How to use an external ID when granting access to your AWS resources to a third party in the AWS documentation.Security and access summary
| Forecasting Role | Optimization Role | |
|---|---|---|
| Applied to | Your management/payer account | Dedicated empty commitment account only |
| Read access | CUR bucket and billing/pricing APIs | No |
| Creates or modifies resources | No | No (purchases commitments only) |
| Accesses workload accounts | No | No |
| Can be revoked | Yes, instantly via CloudFormation | Yes, instantly via CloudFormation |
Security
For a full overview of how Cloud Capital handles data access, encryption, audit logging, and compliance, see the Security page.

